Neural Node 1800019900 Cyber Pulse
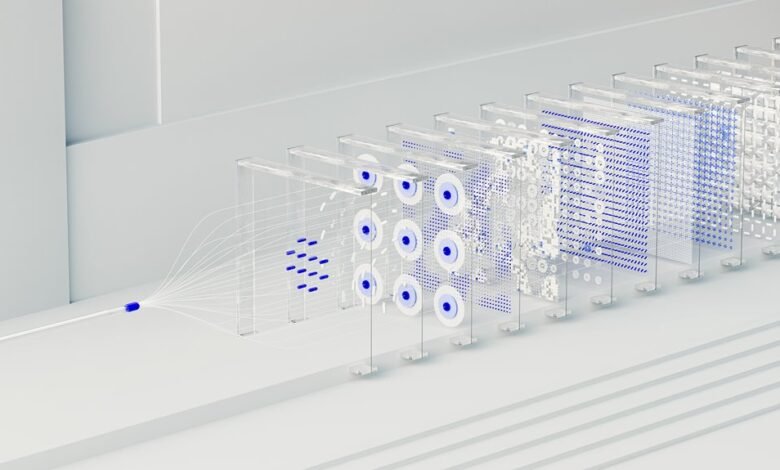
Neural Node 1800019900 Cyber Pulse aggregates telemetry, user interactions, and system signals to form a coherent activity profile. It translates streams into actionable insights while maintaining a wary stance toward opaque governance. Real-time data feeds drive predictions, yet the process invites scrutiny of limitations, biases, and security risks. The architecture implies edge processing and centralized oversight. Questions persist: how transparent are the data pipelines, and who validates the decisions that emerge? The discussion invites closer examination of governance and implementation.
What Neural Node 1800019900 Cyber Pulse Is Really Doing
The Neural Node 1800019900 Cyber Pulse functions as a diagnostic and data-collection system within a networked environment, aggregating telemetry, user interactions, and system signals to produce a cohesive activity profile.
It distills complex activity into actionable insights, yet remains skeptical of opaque governance.
It frames two word discussion ideas: neural pulse, data streams, urging readers toward informed, autonomous scrutiny.
How Real-Time Data Feeds Power Predictive Insights
Real-time data feeds transform raw telemetry into timely predictive signals by continuously updating models with fresh inputs from users, devices, and applications. They underpin cautious optimism about real time data-enabled decisions, yet invite scrutiny of latency, reliability, and bias.
Edge AI and intelligent networks promise localized inference, but dependence on streams may obscure context, demanding rigorous validation for credible predictive insights.
Designing Intelligent Networks: Architecture and Edge AI
The architecture patterns favor modularity, deliberate coupling, and observable interfaces, while edge computing challenges arise from latency, security, and governance.
Critics question overreliance on shards, urging disciplined integration and transparent decision pathways.
Practical Use Cases and How to Get Started With Cyber Pulse
Practical use cases for Cyber Pulse span cybersecurity defense, industrial monitoring, and autonomous decision support, yet clarity is required to avoid overextension beyond demonstrable value.
The analysis remains skeptical, emphasizing concrete outcomes over hype.
Early adopters should prioritize disaster recovery planning and latency optimization, validating benefits through measurable benchmarks before broader deployment, while preserving operational freedom and avoiding vendor lock-in.
Risk-aware experimentation sustains progress.
Conclusion
Neural Node 1800019900 Cyber Pulse operates as a diagnostic ledger and telemetry chorus, translating streams of data into discernible signals. Its predictive leverage hinges on real-time feeds, yet the output remains bounded by governance and transparency constraints. The architecture promises efficiency at the edge, but skepticism is warranted: data shadows, model drift, and governance gaps can erode trust. In essence, Cyber Pulse distills activity into foresight, while demanding disciplined oversight to prevent overreach.